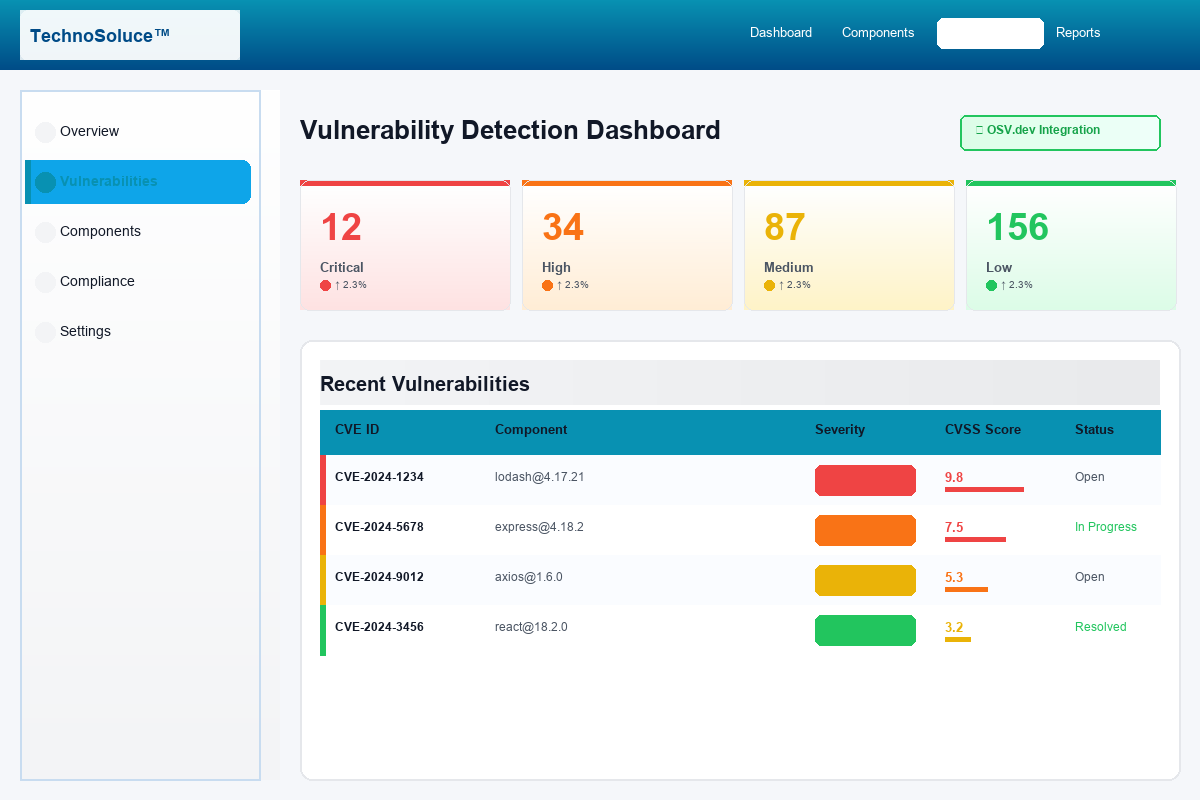
Real-Time Vulnerability Intelligence
Live integration with OSV.dev provides current vulnerability data across all major ecosystems, ensuring you're always protected against the latest threats.
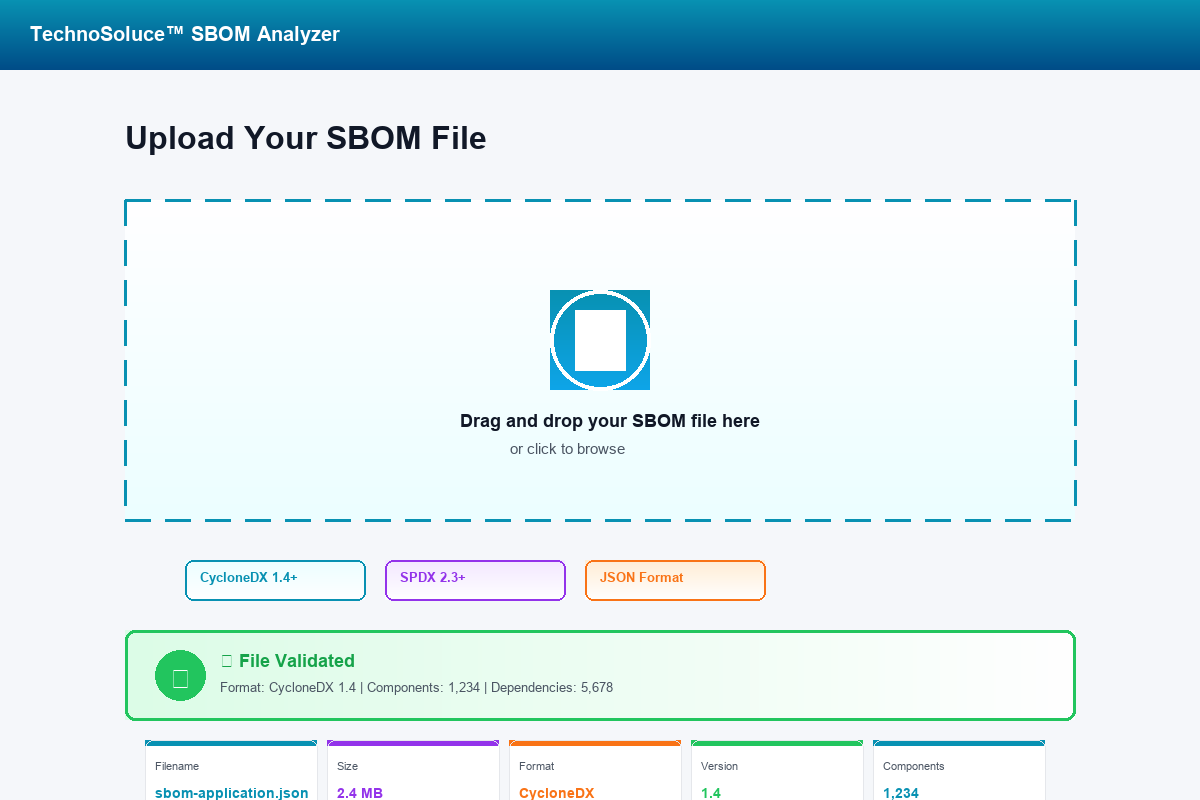
Multi-Ecosystem Coverage
Support for npm, PyPI, Maven, Go, Rust, NuGet, RubyGems, and more. Comprehensive vulnerability data from authoritative sources.
CVSS v3.1 & v2 Scoring
Industry-standard vulnerability scoring with detailed severity classification: Critical, High, Medium, Low.
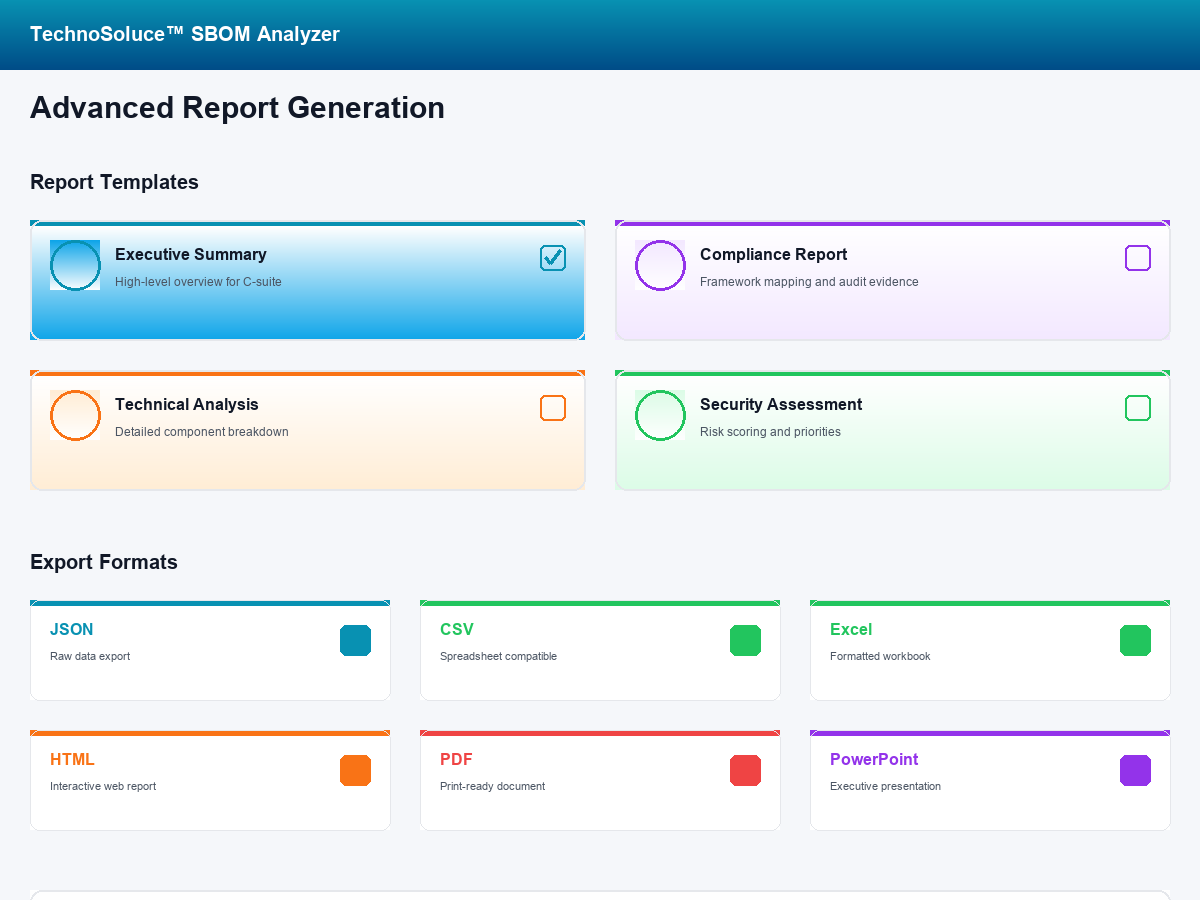
Actionable Remediation Guidance
Detailed fix recommendations, affected version ranges, and patch availability information for every vulnerability.